Firewall Swap & Windows Telemetry Data

I recently switched over from Sophos UTM to Untangle NG for my personal use firewall at home. During the process I basically had to rebuild all of my firewall rules and general network policy configurations. This allowed to me “start fresh” as my previous configuration had gotten quite bloated and complicated over time.
It’s clear that Microsoft has no intentions of telling us what exactly is sent in this telemetry data, how long it’s stored, and why when it’s disabled it continues to send data. Not to mention which obvious third parties have access to the data. For this reason, part of the new network policies I wanted to include was blocking telemetry data from getting sent back to the Microsoft mother-ship.
This is accomplished with Web Filtering and works for both HTTP and HTTPS. I also use a second layer of protection by using OpenDNS domain blocking. That means that if for some reason a request makes it past the web filtering, it will be blocked at the DNS level.
One thing I quickly noticed after blocking these domains was how much they were being used. From the web filtering and OpenDNS filtering combined it adds up to literally tens of thousands of blocked requests and is in the top 10 of my overall DNS requests.
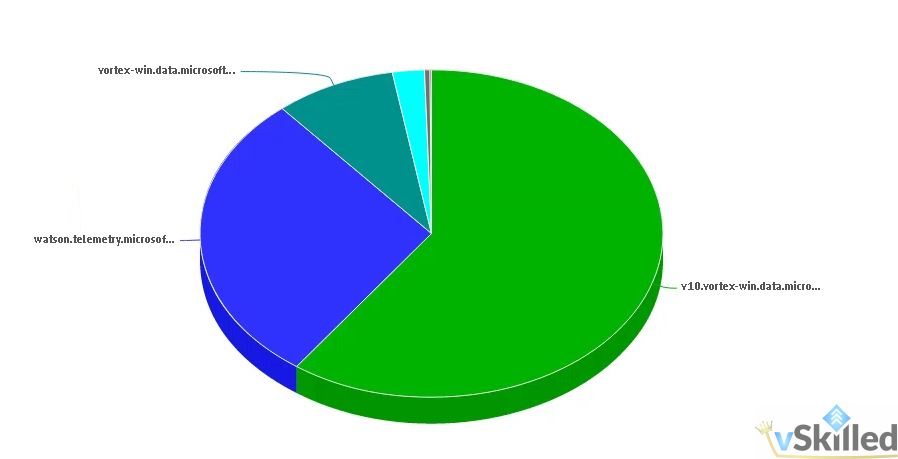
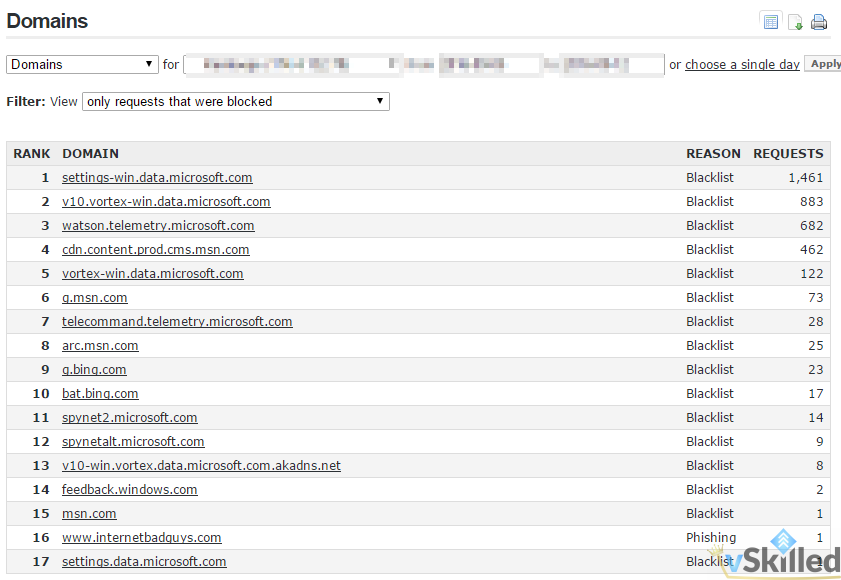
I don’t get it. What and why, especially when I have telemetry set to the lowest collection setting? I cannot imagine the amount and type of data that is sent when it’s set to full! After seeing how much data is collected and how often it attempts to send on low, it gives me reassurance that yes – these domains need to be blocked.
The full list of blocked domains is:
65.39.117.230
23.218.212.69
134.170.30.202
137.116.81.24
204.79.197.200
23.218.212.69
a-0001.a-msedge.net
choice.microsoft.com
choice.microsoft.com.nstac.net
corpext.msitadfs.glbdns2.microsoft.com
corp.sts.microsoft.com
compatexchange.cloudapp.net
cs1.wpc.v0cdn.net
diagnostics.support.microsoft.com
df.telemetry.microsoft.com
feedback.windows.com
feedback.search.microsoft.com
fe2.update.microsoft.com.akadns.net
i1.services.social.microsoft.com
i1.services.social.microsoft.com.nsatc.net
oca.telemetry.microsoft.com
oca.telemetry.microsoft.com.nsatc.net
pre.footprintpredict.com
redir.metaservices.microsoft.com
reports.wes.df.telemetry.microsoft.com
services.wes.df.telemetry.microsoft.com
settings-sandbox.data.microsoft.com
sls.update.microsoft.com.akadns.net
sqm.df.telemetry.microsoft.com
sqm.telemetry.microsoft.com
sqm.telemetry.microsoft.com.nsatc.net
ssw.live.com
statsfe1.ws.microsoft.com
statsfe2.update.microsoft.com.akadns.net
survey.watson.microsoft.com
telecommand.telemetry.microsoft.com
telecommand.telemetry.microsoft.com.nsatc.net
telemetry.appex.bing.net
telemetry.microsoft.com
telemetry.urs.microsoft.com
vortex-sandbox.data.microsoft.com
vortex-win.data.microsoft.com
vortex-sandbox.data.microsoft.com
vortex.data.microsoft.com
watson.live.com
watson.microsoft.com
watson.ppe.telemetry.microsoft.com
watson.telemetry.microsoft.com
watson.telemetry.microsoft.com.nsatc.net

sml156
Have you considered that since you are blocking these domains that instead of Windows trying to connect once a day to say hello I’m here, it will then try to connect every 1 second
Karl Nyen
Do you have a source for this information? A quick capture on Wireshark shows this is false.